NC Protect for Microsoft 365 & SharePoint
Dynamic Data-centric Security for Microsoft 365 apps: SharePoint Online, Office, OneDrive and Exchange

Perimeter Security Alone Doesn’t Work Anymore
With modern collaboration apps, users can access data from an endless variety of locations. Between Azure, Microsoft 365 and other cloud platforms, businesses are adopting new technologies faster than ever and data loss prevention methodology needs to keep up. The data protection policy must be firm enough to manage the risks introduced by cloud services – and flexible enough to allow your users to work when, where and how they want.
Dynamic Data Security for Secure Collaboration in Microsoft 365 & sharepoint
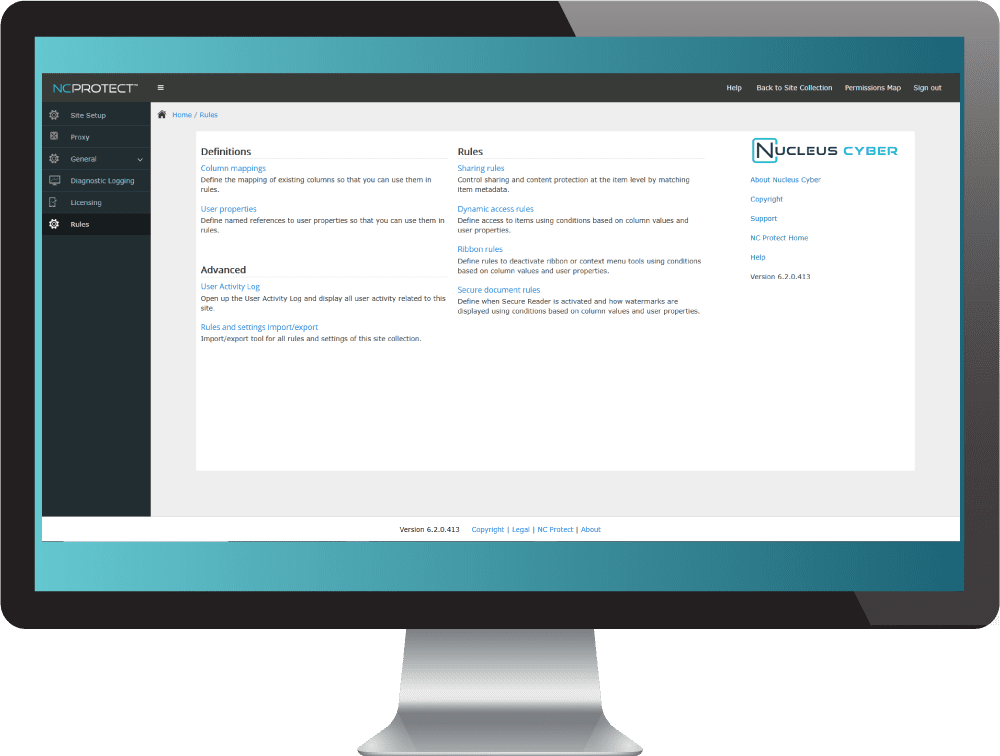
NC Protect provides dynamic data-centric security across Microsoft 365 applications, including SharePoint Online, Office, OneDrive, and Exchange, SharePoint on-premises and Windows file shares, for enhanced information protection in cloud, on-premises and hybrid environments. The platform empowers enterprises to automatically find, classify and secure sensitive data, and determine how it can be accessed, used and shared with granular control using attribute-based access control (ABAC) and protection policies.
It works natively with Microsoft products and enhances security to not just control access to sensitive data, but also apply conditional data-centric protections such as read-only access, user-based watermarks, encrypt or restrict attachments sent through Exchange Email, and more. NC Protect requires no additional client-side application, reducing IT overhead and the risks involved in implementing new cloud services or BYOD policies.
NC Protect delivers data-centric information protection that’s simple, fast and dynamic.






Dynamic, Granular Information security for microsoft 365 apps Without the Complexity

Apply Conditional Access & Security
NC Protect leverages dynamic access, usage denial rules and a secure viewer to ensure that only approved users can access and share your business content. Keep control of your sensitive information on-premises, in hybrid environments or in the cloud. Encrypt or quarantine content when required. Obfuscate data and ribbon actions. Apply protection rules centrally or locally, ensuring compliance, while enabling content experts to fine-tune rules.
Discover & Classify Sensitive Data
NC Protect scans and inspects files in on-premises and cloud collaboration apps for sensitive or regulated data according to defined policies, then automatically classifies it and applies information protection based on its sensitivity and your policies.
It can also leverage Microsoft Purview Information Protection sensitivity labels in combination with other file and user attributes to control access to and apply information protection.
Add unique Data-CENTRIC Capabilities
NC Protect works seamlessly with Microsoft products to augment native security features. It dynamically enforces secure read-only access, hides sensitive files from unauthorized users, redacts sensitive information, applies user-based security watermarks, and encrypts or restricts attachments sent through Exchange Email. It supports common file types, including Word, Excel, PowerPoint, PDF, OCR, CAD files, images, text files and more.

Supports cloud, on-Premises and hybrid
NC Protect provides advanced data-centric security for Microsoft 365 applications, including SharePoint Online, Office, OneDrive, Exchange, and SharePoint Server, for enhanced access control and information protection across cloud, on-premises and hybrid environments.

Reduce Complexity for Faster Results
Get granular security without the complexity of native Microsoft tools to start securing content in hours, not days or weeks. NC Protect requires no additional client-side application, simplifying deployment. It uses a single rule set to efficiently and dynamically control access to content, how authorized users can share it, and with whom across your suite of Microsoft 365 apps.
Audit & Report on FIle Access & Handling
A dynamic Results Viewer provides centralized reporting and management of classified data. Report on the number of issues identified by classification level and allows policy officers to review the results and rescan, reclassify or reapply permissions if needed. Integrate user activity and protection logs with SIEM tools like Splunk or Microsoft Sentinel for further analysis and downstream actions.
Real-Time, Contextual Access Control that Enhances Security Across Microsoft 365 Applications




NC Protect augments native app security in Microsoft 365 applications, including SharePoint, Office, OneDrive, and Exchange, plus on-premises SharePoint, and file shares, using the unique identity data builds over time.
It uses metadata, Microsoft Purview Information Protection sensitivity labels and attributes such as chat content, file name, authorship and date stamps, as well as more transient context like IP location, device or time of day, to apply conditional access and usage rights. Fine grain access and protection policies to support your business rules to secure every collaboration scenario.
NC Protect enforces your data security policies for each user and device, transparently.
Resources
Watch Demo
NC Protect for M365 & SharePoint Data Sheet
NC Protect & Microsoft Information Protection
Customer Success by Industry
Purchase in Azure Marketplace
MACC Eligible
Experience NC Protect. Request a Demo.
See how NC Protect enables simple, fast and dynamic data-centric security for M365.