Resource Center
Filter by
All Resources | Kojensi Resources | NC Protect Resources

White Paper: ITAR Compliance Checklist
A guide to compliance and information security requirements and best practices for achieving ITAR compliance.
Solution Brief: NIST SP 800-162 ABAC Model
Explore how NC Protect implements Attribute-Based Access Control (ABAC) capabilities following the NIST SP 800-162 ABAC model to enhance and complement your existing Microsoft security framework.

White Paper: CMMC 2.0 – Jumpstart FCI & CUI Protection with Data-Centric Zero Trust
Explore how extending a Zero Trust approach to file access and sharing ensures compliance with the CMMC 2.0 standards that map to NIST 800-171 and NIST 800-53 for secure and compliant collaboration of FCI and CUI.

eBook: The BYOK Gap in Microsoft Azure and M365
Understanding the potential risks of retaining encryption keys with Cloud Service Providers (CSP), including Microsoft Azure and Microsoft 365 (M365),
that can lead to data exposure and non-compliance with GDPR and other data protection laws.
eBook: Complying with Australia’s SLACIP Act & SONS Regulations for Critical Infrastructure
Risk management and governance are critical to SLACIP and SoNS, however, enforcing these mandates is another matter. Explore who these regulations impact, what is required and how to quickly stand up secure and compliant information sharing in this eBook.

Datasheet: NC Protect Janusseal Documents Connector
Learn how NC Protect's Janusseal Documents integration allows customers to leverage existing Janusseal classifications as part of the attributes used for enacting NC Protect’s dynamic ABAC policies.

Datasheet: NC Protect for NetApp ONTAP
Explore how NC Protect with ONTAP addresses the protection of information, dynamically at the data layer at the time of access to provide a multi-faceted, 360-degree layered approach to protecting data that is accessed on Windows File Shares in ONTAP.
Webinar: 5 Steps to Prepare SharePoint Data Before Migrating to M365
In this webinar, we share 5 key steps to prepare your data in SharePoint on-premises before you migrate to ensure a smooth transition to M365 and SharePoint Online.
Case Study: A Master Class on Digital Transformation and Data Security with NC Protect
Discover how archTIS’ NC Protect offers a solution to secure Skool4Kidz digitised curriculum in M365 with in-transit encryption and unique security capabilities.

Guide to Controlled Unclassified Information (CUI) Markings
Download this guide to understand the US DOD's new controlled unclassified information (CUI) marking requirements and how to automate the process.

Datasheet: Kojensi Saas for the Defence Industry
Discover how the Kojensi Federal government accredited SaaS platform enables the Defence Industry to securely share and collaborate on sensitive information up to PROTECTED with Defence and industry partners.

Webinar: Addressing Digital Sovereignty & Key Management Challenges
Recently, archTIS worked with fellow MISA member, Thales, to integrate CipherTrust Manager with NC Encrypt to offer a viable solution for customers using Microsoft 365 that are determined to keep their keys separated from their data in the cloud. In this recorded webinar archTIS and Thales showcase the advantages for customers aiming to achieve digital sovereignty.

What is Attribute Based Access Control or ABAC?
Watch this short video to learn about the advantages of using ABAC-enabled access and data protection policies to better safeguard sensitive data from improper access, misuse and theft.
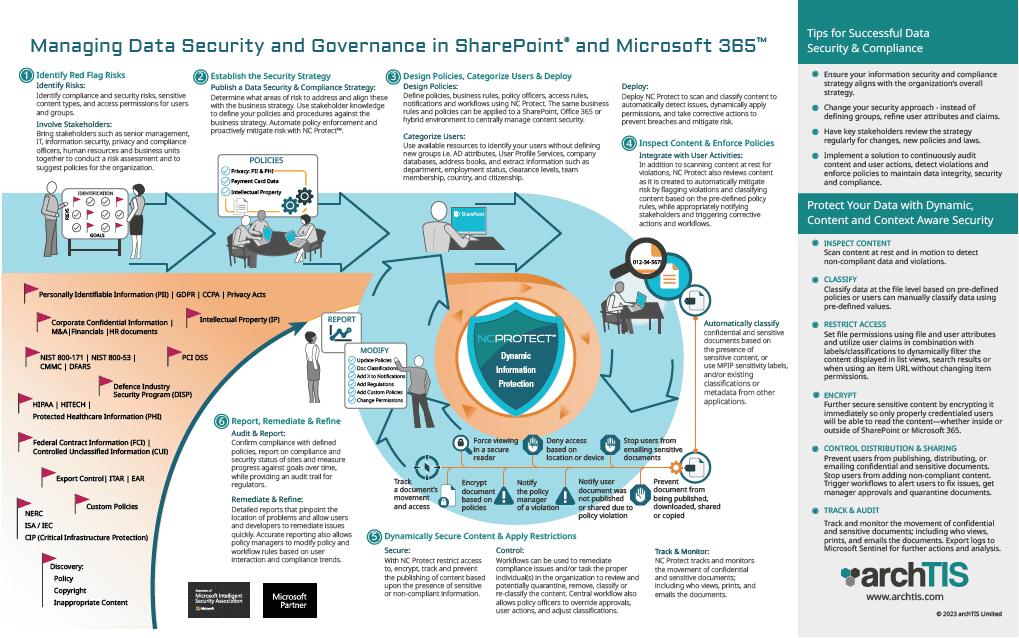
Infographic: Managing Data Security and Governance in Microsoft 365 & SharePoint
Get the steps for effectively manage data security and governance; from defining your strategy to using NC Protect to enforce compliance and apply dynamic security to Microsoft 365, SharePoint Server and file share content.
Webinar: Protect Sensitive Data with Microsoft Purview Information Protection & ABAC Policies
archTIS’ Dave Matthews and special guest Microsoft's Director, Director, Compliance and Privacy Ecosystem, Hammad Rajjoub, discuss how to enhance information protection controls to guard your most vital assets and ensure they don’t accidentally or deliberately walk out the door.

Datasheet: Kojensi for Government
Explore how Kojensi provides a faster, more efficient process for Government to securely share and collaborate on sensitive or Protected information internally and with partners.

Datasheet: Kojensi for Multinational Coalitions
Learn how Kojensi empowers Multinational coalition partners to share and collaborate on highly classified information with different security models on a single platform.
Datasheet: Kojensi for University Defence Research
Learn how to enable secure collaboration of sensitive and classified research between Universities, Government, Defence and Industry partners with Kojensi.
